You're typing away in an online code editor, maybe testing a quick API integration or debugging a database connection. You drop in a placeholder API key or a dummy password, thinking it's just local, temporary, safe. It's not saved, right? It's just in your browser. Here's the uncomfortable truth I discovered through testing: for many of these platforms, that assumption is dangerously wrong. The moment your fingers hit the keys, your code—including every secret you typed—can be on its way to a remote server.
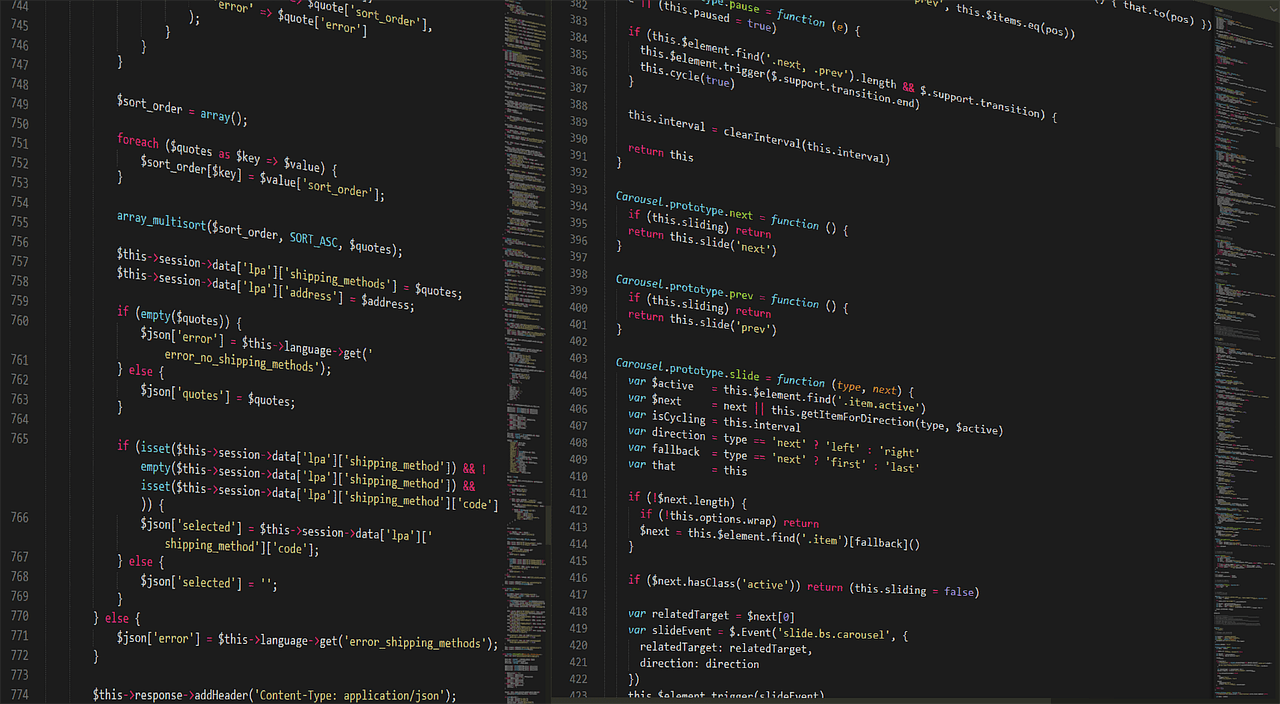
This isn't theoretical. I planted fake credentials like const API_KEY = "sk-secret-test-12345" in various online editors and watched the network traffic. The results, particularly from CodePen, were eye-opening. Your development workflow might be leaking secrets you never intended to share. Let's break down what's happening, why it matters, and most importantly, how you can code safely in the cloud in 2026.
The Real-Time Transmission You Never See
When you think about saving code online, you probably picture clicking a "Save" button, triggering a single, deliberate request. The reality with modern, feature-rich editors is far more continuous. To provide instant previews, live error checking, and collaboration features, these tools need to process your code constantly.
My test was simple: open CodePen, start a new pen, and type the fake keys. With the browser's developer tools open to the Network tab, I didn't even have to finish the line. The instant I typed the closing quote on that API key string, POST requests fired off to CodePen's endpoints. Specifically, traffic went to codepen.io/cpe/process (which handles Babel transpilation) and codepen.io/cpe/boomboom/store (for preview rendering).
This isn't a bug—it's how the feature works. The live preview pane updating as you type? That requires sending the code to a server to process it and return the result. The auto-saving draft functionality? Same deal. The system is designed for convenience and immediacy, but that design has a significant side effect: there is no "local only" state for your unsaved work. From the platform's perspective, as soon as it's in the editor, it's fair game for transmission.
What Exactly Gets Sent?
It's the entire payload of your editor pane. Not just the line you're editing, but everything. In my tests, the POST request bodies contained the full HTML, CSS, and JavaScript code, neatly packaged in JSON. My fake sk-secret-test-12345 key was there in plain text, along with the dummy database password. No obfuscation, no encryption specific to that sensitive string—just your raw code, traveling over the wire to CodePen's infrastructure.
And think about the context. This happens while you're still figuring things out. This is the phase where developers often use real keys from a test environment or, worse, accidentally paste a production key to see if a connection works. The assumption that "I haven't saved it yet" creates a false sense of security that the architecture simply doesn't support.
Why This Architecture Exists (It's Not Malicious)

Before we grab our pitchforks, it's worth understanding why platforms are built this way. It's almost never a case of a company trying to sneakily harvest API keys. The driving forces are user experience and technical necessity.
First, the live preview. To show you what your code renders to in real-time, the platform needs to execute it. For security and resource management, that execution typically happens in a controlled, sandboxed environment on a server, not in your browser. Your code goes up, it runs in a container, and the result (HTML, console logs, errors) comes back down. This is especially true for code that requires compilation or transpilation, like JSX or TypeScript.
Second, auto-recovery. How many times have you lost code because a browser tab crashed? Auto-save drafts are a lifesaver. To implement that, the editor needs to periodically send your work to a persistent store. The line between "periodically" and "continuously" has blurred to the point of invisibility.
Third, collaboration. Tools like live multiplayer editing, where multiple cursors are visible, require a central server to synchronize state between all clients. Every keystroke becomes an event that needs broadcasting.
The problem isn't the intent—it's the lack of clear communication and safeguards around this model. Most developers using these tools are completely unaware of the data flow. The privacy policy might cover it in legalese, but the real-time UI doesn't signal "everything you type is being sent elsewhere."
Beyond CodePen: The Ecosystem's Privacy Spectrum
CodePen was the standout in my tests for its immediacy, but it's part of a broader landscape. I tested others, and their behaviors varied. This isn't a universal condemnation of all online editors, but a call to understand their individual privacy postures.
Some editors, particularly those that market themselves as full-fledged IDEs in the cloud (like GitHub Codespaces, GitPod, or Replit in certain modes), may execute code within a dedicated, isolated virtual machine or container that you "own" for the session. The transmission still happens, but the boundary of trust is different—it's your workspace, not a shared processing pipeline. The risk shifts from exposure to the platform to the security of that isolated environment.
Other simpler editors might do more processing client-side. A basic HTML/CSS/JS preview can often be rendered directly in your browser using an iframe and srcdoc, without a server round-trip. These pose a much lower risk of transmitting secrets externally. The challenge is knowing which is which.
Then there's the question of what happens to that data on the server. Is it logged? For how long? Who has access? Is it scanned by automated systems? These are the questions the original Reddit thread exploded with. Many developers shared stories of getting automated security alerts from GitHub or other services because they'd accidentally committed a key to a private repo. If automated scanning is happening on private repositories, it's certainly plausible on the data streams of online editors, even if just for abuse prevention.
Practical Defense: How to Code Safely in Online Editors

Okay, so the risk is real. But online editors are incredibly useful. Abandoning them isn't practical. Instead, we need to adopt safer practices. Here's what you can do, starting today.
1. Use Environment Variables, Even for Dummies. This is the single most effective habit. Never hardcode secrets, even in throwaway code. In your online editor, use placeholders and treat them as if they were environment variables. For example, instead of const API_KEY = "real_key_here", write const API_KEY = process.env.API_KEY || "MISSING_API_KEY_PLACEHOLDER". It forces the right mental model. For the preview to work, you might need to create a mock configuration object, but keep the real values entirely out of the editor pane.
2. Leverage Client-Side Only Tools for Sensitive Prototypes. If you're just testing an idea with real credentials, consider using a tool that runs 100% in your browser. Local-first editors like VS Code with the Live Server extension can give you a similar rapid feedback loop without any data leaving your machine. For quick HTML/CSS/JS sketches, sometimes a local file and your browser are the most secure tools available.
3. Employ Fake Data Generators Rigorously. Make it a rule: online editors get fake data only. Use libraries or patterns to generate realistic-but-fake credentials. For API keys, use a format that mimics your real provider (e.g., sk_test_51[random chars]) but is clearly invalid. For database connections, use localhost or dummy cloud URLs. This preserves the utility of the editor for logic and structure testing without the exposure.
4. Audit the Network Tab Yourself. Don't take my word for it. The next time you use an online editor, open your browser's Developer Tools (F12), go to the Network tab, and watch what requests are made as you type. Look for POST requests to external domains. This firsthand knowledge is powerful. You'll see exactly what data is being sent and where.
What Should Platform Developers Do?
This isn't just on the individual developer. Platform creators have a responsibility here. The community in the original discussion had several clear demands.
Transparency is Key. There should be a clear, visible indicator in the UI when code is being transmitted to a remote server. A small icon that lights up with "Syncing..." or "Processing remotely..." would go a long way. The privacy policy should explicitly state this behavior in plain language, not buried in a terms of service document.
Offer a "Local Preview" Mode. For code that doesn't require server-side compilation, give users an option to disable remote processing. The preview might be slightly less accurate or lack some features, but for sensitive work, it's a trade-off many would welcome.
Implement Client-Side Secret Obfuscation. Before sending the code payload, the editor could scan for common patterns (like API_KEY, password, secret in variable names or common formats like Stripe keys) and replace the values with placeholders or hash them for the transmission. The real value would only exist in the browser's memory. This is a technical challenge, but a worthwhile one.
Clear Data Retention Policies. Be explicit about how long draft code is stored on servers, who can access it, and when it's purged. Many developers would be more comfortable if they knew this data was held ephemerally, just for the live preview, and not written to permanent storage.
Common Misconceptions and FAQs
Let's address some of the recurring themes from the online discussion.
"But it's over HTTPS, so it's fine, right?" HTTPS encrypts the data in transit between you and the platform's server. It protects you from eavesdroppers on the network. It does not protect the data from the platform itself once it's received. The platform's servers see the plaintext data.
"I only use free/test keys anyway." This is better than leaking production keys, but it's still a risk. Test keys often have permissions and can incur costs. They can also be used to probe your infrastructure or as a stepping stone. A leaked test key is a security incident.
"Isn't this just like using any SaaS product?" There's a difference in expectation. When I type into Google Docs, I know my document is being saved to the cloud. The primary function is storage and collaboration. With a code editor, many developers perceive the editing pane as a temporary, local workspace until they explicitly save or share. The paradigm clash is the issue.
"Can't they just scrape my screen anyway?" This is a more paranoid take, but technically harder. Transmitting specific code payloads is a structured, intentional part of the application's architecture. Unauthorized screen scraping would be a major breach of trust and likely illegal. The former is a design flaw; the latter is malware.
The Bottom Line for Developers in 2026
The convenience of online code editors is undeniable. They lower barriers to learning, prototyping, and sharing. But in 2026, as these tools become more powerful and integrated into our workflows, we must shed the illusion that they work like local applications.
Treat every online editor as a public space by default. Assume every keystroke could be logged, transmitted, or stored. This isn't to scare you away from using them—it's to encourage you to use them smartly. Adopt the practice of never putting real secrets into them. Use environment variable patterns, fake data, and client-side alternatives when needed.
Finally, use your voice as a community. When choosing a tool, consider its privacy model. Ask the developers about their data handling. The more we demand clarity and safety-by-design, the better these essential tools will become. Your code is your responsibility, but the platform's job is to not make that responsibility harder than it needs to be.
Go ahead, fire up that CodePen or JSFiddle for your next idea. Just remember: what happens in the browser doesn't always stay in the browser. Code accordingly.