The Digital Age Dilemma: Separating Signal from Noise
You've seen the headlines. The explosive claims. The screenshots that spread like wildfire across social media. In 2026, we're drowning in information but starving for truth. When sensational stories break—especially involving high-profile figures—the immediate reaction is often emotional rather than analytical. But here's the thing: technology gives us unprecedented power to verify or debunk claims, if we know how to use it.
I've spent years testing verification tools and methods, and what I've learned is this: most people don't know where to start. They see a "leaked email" or "confidential document" and take it at face value. That's dangerous. Really dangerous. The tools to investigate these claims are often free, accessible, and surprisingly powerful. You just need to know they exist and how to use them.
This isn't about any specific claim or person. It's about developing a skill set that serves you across every controversial story you'll encounter online. Let's build that toolkit together.
Understanding the Source: More Than Just a URL
When that Reddit thread blew up with thousands of upvotes and hundreds of comments, the first mistake people made was focusing on the sensational content rather than the source. The Financial Times article referenced was paywalled—immediately creating a barrier to primary source verification. This is a classic technique: reference a credible outlet but make the actual content inaccessible, forcing reliance on secondary interpretations.
In my experience, you need to approach every viral claim with three source questions: Who's sharing it? Where did it originate? And what's their track record? The Reddit community actually did a decent job of this—multiple commenters pointed out the need to see the actual emails, not just summaries. That's the right instinct.
One user noted: "Without seeing the actual emails, this is just hearsay." Exactly. But here's where technology helps. Tools like the Internet Archive's Wayback Machine can sometimes bypass paywalls for historical articles. Browser extensions that detect tracking parameters can show you if a link has been modified. And simple WHOIS lookups—though less revealing since GDPR—can still give you basic domain registration information.
The key is moving from "this sounds plausible" to "here's how I verified the source." It's a mindset shift that changes how you consume information.
Email Forensics: What You Can Actually Verify
Let's talk about the specific claim format here: alleged emails. Email verification has become surprisingly sophisticated. When someone claims "emails show X," you should immediately think about metadata. Genuine email headers contain a treasure trove of verifiable information: sending and receiving servers, timestamps (in UTC, which is important), message IDs, and sometimes even geographic data.
There are legitimate tools for this. Microsoft's own Message Header Analyzer (a free web tool) can parse complex email headers from Outlook. For Gmail, you can view full headers natively and use third-party analyzers to make sense of them. The point isn't that you'll become a forensic expert overnight—it's that you should know what's possible.
Several Reddit commenters asked the right technical questions: "Are these emails authenticated?" "What's the chain of custody?" "Has anyone verified the digital signatures?" These aren't abstract concerns. In 2026, PGP and S/MIME email encryption are more common, especially among people who might be targets of hacking. A legitimate leak often includes cryptographic verification.
What most people don't realize is that you can often verify email authenticity without seeing the content. The metadata alone can tell you if emails were actually sent between the claimed parties at the claimed times. If that metadata is missing or suspicious, the entire claim collapses. It's like checking the foundation before buying the house.
The Automation Advantage: Scaling Your Verification
Here's where things get interesting. When you're dealing with large document dumps—like the thousands of pages in the Epstein case—manual verification becomes impossible. This is where automation tools shine. I've used several approaches over the years, and while I can't recommend specific tools for analyzing legally sensitive material, I can tell you about the categories that exist.
Document comparison software can identify inconsistencies in formatting, fonts, and metadata across supposedly related documents. Timeline analysis tools can visualize claimed sequences of events and flag chronological impossibilities. And text analysis platforms can identify writing style patterns that might suggest forgery or multiple authors.
One approach I've found particularly effective is using automated data extraction tools to gather related information from multiple sources for comparison. When you're trying to verify a claim, you often need to pull data from news archives, public records, and other databases. Doing this manually takes weeks. Automation can do it in hours, giving you a much broader context for evaluation.
But—and this is crucial—automation doesn't replace human judgment. It amplifies it. You still need to interpret the results, understand their limitations, and recognize when the tool might be missing nuance. The best verifiers I know use technology as a magnifying glass, not a crystal ball.
The Human Element: Why Context Matters More Than Ever
Reading through those 228 Reddit comments, what struck me was how many people focused on technical verification while missing psychological and contextual factors. One astute commenter noted: "The timing of this 'leak' is suspicious given current events." Another pointed out: "This follows a pattern of similar allegations that never seem to have verifiable evidence."
This is where technology meets psychology. In 2026, we have tools that can analyze timing patterns in news cycles, track how narratives evolve across platforms, and even identify coordinated amplification campaigns. Services like CrowdTangle (though its future is uncertain) and other social listening platforms can show you how a story spreads, who amplifies it first, and what communities pick it up.
I always ask: What happens if this claim is true? What happens if it's false? Who benefits in each scenario? This isn't conspiracy thinking—it's basic media literacy. The Reddit discussion actually showed good media literacy instincts. Multiple users questioned why certain outlets were running with the story while others ignored it. They noted the lack of named sources. They asked about possible motivations.
The technology here isn't fancy. It's simple pattern recognition, aided by tools that help you visualize information flows. Sometimes the most powerful verification tool is a calendar and a notepad, tracking when claims emerge relative to other events.
Practical Verification Workflow for 2026
So how do you actually do this? Let me walk you through my personal verification workflow when I encounter a sensational claim. I've refined this over hundreds of investigations, and it works whether you're looking at political claims, celebrity gossip, or business allegations.
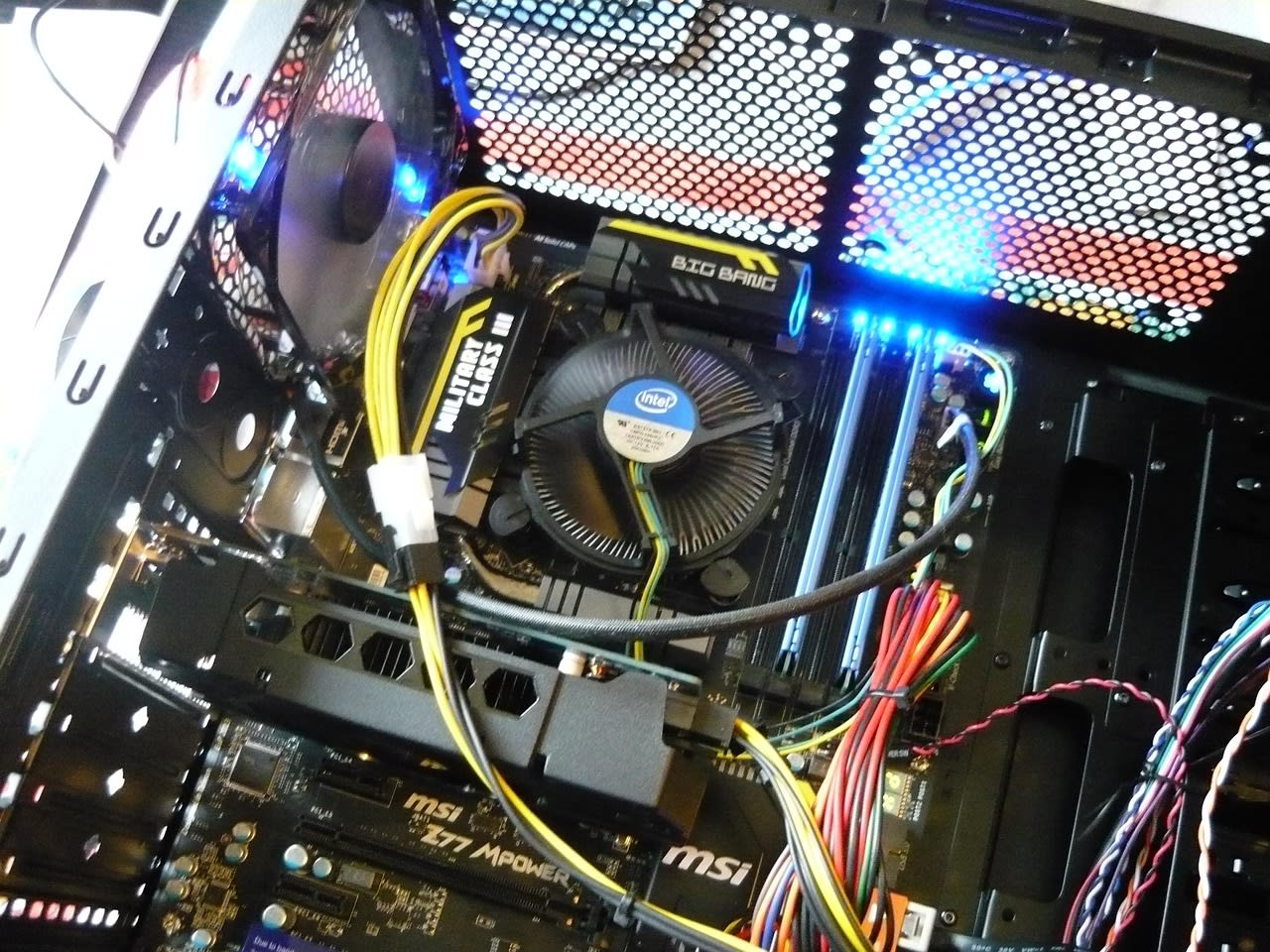
First, I capture everything. Screenshots, URLs, usernames. I use Portable External Hard Drive to store original files separately from my main system. Organization matters—create dated folders with clear naming conventions.
Second, I go upstream. Where did this information first appear? Not where it went viral, but where it originated. Reverse image searches, keyword tracking, and archive services are your friends here. I often use multiple browsers—sometimes with VPNs—to see if content appears differently in different regions.
Third, I check the technical artifacts. For emails: headers, domains, timestamps. For documents: metadata, editing history, format consistency. For images: EXIF data, compression artifacts, source lighting analysis. Free tools like FotoForensics can reveal digital manipulation that's invisible to the naked eye.
Fourth, I seek contradictory evidence. This is the hardest step psychologically. We want to confirm our initial reactions. But the most important question is: What evidence would prove this wrong? If I can't find any, that's actually a red flag. Genuine claims usually have some counter-evidence or alternative explanations that need to be ruled out.
Finally, I document my process. Not just my conclusions, but my steps. What tools I used, what searches I ran, what assumptions I made. This creates accountability and allows others to replicate or challenge my work.
Common Mistakes and How to Avoid Them

Let's be honest—we all make verification mistakes. I've certainly made my share. But learning from common errors can save you enormous time and credibility.
The biggest mistake? Confirmation bias. We tend to seek information that confirms what we already believe. The Reddit comments showed this in both directions—some immediately accepted the claims because they fit existing narratives, others immediately rejected them for the same reason. Technology can help here: use tools that deliberately surface opposing viewpoints. Browser extensions that show you left/right coverage of the same story. News aggregators that include international sources.
Second mistake: Over-reliance on single tools. I've seen people declare something "verified" because one tool gave them a green light. But tools have limitations. Email header analyzers might not catch sophisticated spoofing. Image verification tools can be fooled by AI-generated content. The solution is tool diversity—use multiple methods and see if they agree.
Third: Ignoring the human element. Several Reddit commenters shared personal experiences with STD testing, privacy concerns, or relationship dynamics. While these aren't "technical" verification, they provide important context about what's plausible versus what's sensational. Sometimes the best verification question is simply: "Does this make sense given how people actually behave?"
Fourth: Time pressure. Viral claims create urgency. You feel you need to decide NOW. But verification takes time. My rule: the more urgent a claim feels, the more slowly I proceed. If it's truly important, it will still be important tomorrow after proper verification.
Building Your Personal Verification Toolkit
You don't need expensive software to verify claims effectively. Here's what I actually use in 2026, divided by category and availability.
For document analysis: LibreOffice (free) actually has decent metadata examination tools. For PDFs, Adobe's own preview tools show creation dates and editing history. For more advanced needs, hiring a digital forensics specialist for a few hours can be surprisingly affordable and can give you professional-grade analysis.
For image verification: Google Reverse Image Search is the obvious starting point. But don't stop there. TinEye has a different database. Yandex's image search sometimes finds different matches. And for deep analysis, the free online tool Forensically offers clone detection, error level analysis, and metadata extraction.
For email analysis: Besides the tools mentioned earlier, consider email privacy test services that can show you what information your email client leaks. ProtonMail's security features are worth studying even if you don't use them—they show what's possible with modern email security.
For information gathering: Digital Notebook devices can help organize your research without the distractions of a full computer. For software, note-taking apps with tagging and linking capabilities (like Obsidian or Roam Research) let you connect related information in ways that reveal patterns.
The most important tool? A healthy skepticism. Not cynicism—skepticism. The willingness to ask questions, demand evidence, and change your mind when new information emerges.
The Future of Verification: What's Coming Next
As we look toward the rest of 2026 and beyond, verification technology is evolving in fascinating directions. Blockchain-based timestamping services are becoming more accessible, allowing anyone to cryptographically prove when they created or received a document. AI detection tools are improving (though still imperfect) at identifying machine-generated text, images, and videos.
Perhaps most importantly, we're seeing a growing ecosystem of independent verification organizations. These aren't traditional fact-checkers but technical analysis groups that specialize in digital forensics. Some offer their services to journalists and the public at reasonable rates.
The Reddit discussion actually hinted at this future. Several users suggested crowd-sourced verification—distributing analysis across multiple people with different expertise. With proper coordination and tooling, this could become incredibly powerful. Imagine a platform where technical experts, subject matter experts, and investigators collaborate on verifying complex claims.
What won't change is the human element. Technology can give us data, but we still need wisdom to interpret it. The ability to ask good questions, recognize our own biases, and communicate findings clearly—these skills will only become more valuable as our tools become more powerful.
Becoming a Verification-First Consumer
Here's the bottom line: In 2026, verification isn't a specialized skill for journalists and investigators. It's a basic literacy for anyone who consumes information online. The tools exist. The methods are learnable. The only thing missing is the habit.
Start small. Next time you see a sensational claim, take five minutes to ask: What's the actual source? What evidence is presented? What's missing? Use one verification tool you haven't tried before. Document what you find.
What I've learned from years of doing this work is that verification changes how you see the world. You become less reactive, more thoughtful. You recognize patterns in misinformation. You develop a healthier relationship with information itself—seeing it as something to be examined rather than simply consumed.
The alternative is to be perpetually buffeted by whatever viral claim comes next. To live in a state of constant outrage or confusion. To have your attention and emotions manipulated by those who understand that most people won't verify.
You have a choice. You can be part of the noise, or you can be part of the signal. The technology exists to help you choose wisely. Your attention—and your understanding of truth—are worth protecting.




